Over time, users are more and more aware the importance of digital security measures that prevent others from accessing your personal information; and that protect content that you post or store on local devices. All the more so when information such as the massive Facebook and LinkedIn leaks (initially denied) and others emerge.
That is why we are going to dedicate this article to say What exactly are two-factor authentication apps and how they work, and also to offer the most popular options that can be found at the moment, through Google’s own app. So, let’s dive into the world of two-step authentication.
What is two-step authentication

We are already very used to having to do a repetitive task when we access an online service, although many of them store the session and only ask us to repeat the process every now and then: we enter the web or the application in question, we enter a username and password and the service gives us access to the interior, knowing at all times that it is we who are accessing it.
But this process is a single user identification step, and there are other methods known as two-step authentication, although not all services offer it. This authentication consists of sewing the first step a second which involves enter a second code, a second password which is generated automatically for the moment
So, if someone were to decipher our username (or our email, or our phone number) and our access password, they would still need this second key which, as they say, is generated automatically. depending on certain keys and that, therefore, it is practically impossible that it is stolen from us. Although there is no 100% secure identification system, it is convenient to know.
It is at this stage that it is necessary to notify that SMS authentication is also not secure, because there have already been several thefts of SMS identifiers with which to bypass this system by information thieves. We always recommend and will recommend specific apps for two-step authentication, and we’ll recommend more later.
How two-step authentication apps work
We have already said that not all online services offer this possibility, but the most popular such as Facebook, Instagram or Twitter, among others, do. The operation between all is practically identical: once we activate it in the aforementioned service, we are given a QR code or a text code to enter in the corresponding authentication application, and this is what will allow each access key to be generated later.
Thus, we already have the first security factor, namely that the service in question (Facebook, Instagram, Twitter or other) generates an authentication code valid only for our account. This code is then completed by an algorithm that does not vary and with a seed that changes periodically, so that each final key generated is unique at every moment.
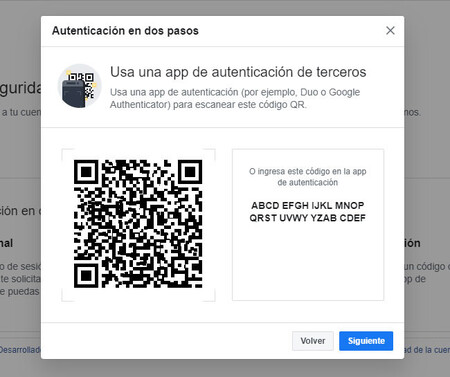
The other seed we were talking about is time. If we use a two-step authentication app, we’ll see that the passcodes they offer us change every thirty seconds. The application takes the time that the key has been requested, mixes it with the initial key provided by the service, and runs a series of complex mathematical algorithms to, in the end, give us a valid access key. And after 30 seconds the password changes. And after 30 seconds a new one.
The service provides us with a unique initial key and the application generates another which changes every few seconds
Since we have already entered at the time the key offered by the online service, the algorithm is inserted into the application and the temporary seed is obtained simply by checking the time, These applications work without the need to be connected to the Internet. Thus, we can easily install them on devices that are not logged in, which makes accessing our secret key infinitely more difficult, as external attacks cannot be suffered.
So we open our app, enter our username and password, then enter the second password that the two-step authentication app gives us, and we’re already inside. Double security and one of the keys generated from secret codes
The best two-step authentication apps for Android
Now is the time to recommend the best two-step authentication apps that we can find in the Android ecosystem, and maybe they’ll be present on iOS as well if we want to look for them there too, as we’ll be talking about apps. popular with a lot of weight among users. And of course you must start by recommending Google Authenticator.
Google Authenticator

Google Authenticator is an application created by Google and used to provide codes that you can use to verify your identity after entering your username and password. It can be used to improve the security of your Google Account, but is compatible with a multitude of services like Facebook, Amazon and Hotmail.
Google Authenticator
Authy

Another of the most popular and robust options in the two-step authentication world is the one offered by Authy, perhaps not as popular as Google’s native tool but also compatible with a plethora of apps and of online services. Authy also has a double security in itself since it gives us the possibility of block access to the application with a fingerprint, so it makes sure we’re the ones using it. Very recommendable.
Twilio Authy 2-factor authentication
Microsoft Authenticator

A two-step or two-factor authentication app that also comes highly recommended is the one made by Microsoft, which is also cross-platform, so it’s easy to find it wherever we look for it. It also allows us set fingerprint or face to access the app, adding an extra layer of security to using the app itself.
Microsoft Authenticator
Table of Contents