Programs keep making continuous memory requests, as they send hardware not only to process data, modify it, create new data, delete existing data, etc. But, there are sections of memory that if a program accesses it can end up disrupting the overall functioning of the system. We call this memory protection.
At some point in their evolution, processors began to implement memory protection systems that separated RAM addressing into several sections. To understand this, it suffices to imagine that there is a district for exclusive use in a city and a police force which prevents access to said district to those who cannot use it, citizens having the privilege of use all operating system processes. .
Why is memory protection necessary?
Memory protection became necessary in PC processors as soon as it became necessary to create multitasking environments in which several programs shared memory access at different times. The early years of computing were with single-task programs that also performed the task of the operating systems themselves at the same time, especially on 8- and 16-bit home computers based on the MOS 6502 and Z80A.
A famous case for the lack of memory protection in the processor, we have it in the classic Commodore Amiga, whose versions based on the 68K standard had continuous crashes due to running an operating system multitasking on a processor without memory protection, as happened with the Apple Macintosh under the same processor.
Today, all processors have built-in memory protection, having to run very complex multitasking operating systems where the number of concurrent processes is in the thousands.
How does memory protection work?
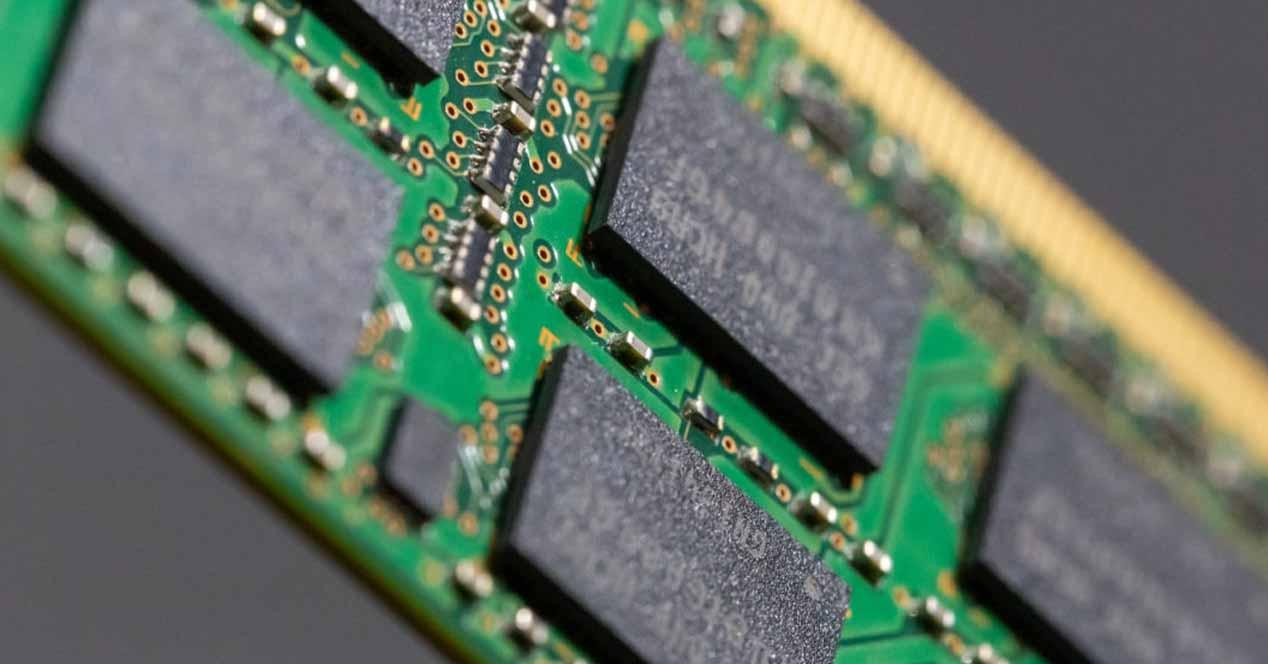
In contemporary processors, memory protection is provided by the same processor, in order to avoid headaches for developers. Each CPU has stored in a series of registers what is called the page table, which informs it of the organization of system memory. The page table is not only used to translate virtual memory addresses to physical memory, but also which part of memory is accessible by applications and which is not.
When an application accesses a portion of memory that it is not authorized to do, the CPU then generates an interrupt which gives control to the operating system. From there it depends on how the solution has been implemented at the software level. The operating system can decide to completely stop the program and all of its processes unilaterally.
It must be taken into account that the page table contains not only information on the organization of the memory, as well as its privileged access parts, but also the situation of the RAM at all times. It is managed by a kernel thread of the operating system, which is responsible for allocating the various resources to active programs, either in the form of CPU execution time or memory access.
Veto programs
RAM under the vision of all current processors is divided into pages and not memory addresses. Which are translated into physical memory addresses by the memory management unit. But what happens when part of a program performs illegal memory access? We have already explained the process, but to prevent the CPU from going into an absurd loop, what is done is to mark a bit in the virtual address that the binary that is stored is not a program but data.
So that when the CPU returns to these virtual memory addresses, it no longer does so as if it were a program, but as a set of data that it ignores. Obviously, if there is a program with a jump instruction to this memory address, an error will occur, but the code that tried to access the RAM will no longer be executed.
This bit on x86 processors is called the No-Execute or NX bit. This is a very simple security measure that the operating system can handle, but it is not the only one that an operating system has to prevent the execution of invalid code. Although the protection mechanism does not always work and there are other mechanisms with which the processor obscures the protected memory to the applications.
For example, the operating system assigns itself an exclusive access bit for all of its threads. When an application without its privileges is granted access to the protected RAM by modifying the access bit, the operating system resets this bit by manipulating the section that corresponds to the applications in the page table.
How does the CPU get the page table?
The first program to run on a PC, regardless of its format, is the operating system. Some more complex systems load a preview system that powers on the hardware and passes the testimony to the operating system in disguise. This process is not hardware dependent, but all hardware has a memory address where it starts and from there it goes through memory one way or another depending on whether it is a Big Endian processor. or Little Endian.
Therefore, in these memory addresses there must be the information to start the PC, which today is UEFI but in its early days it was BIOS. Which acts as an opening act for the operating system. But where does the operating system pull the RAM situation? Well, it does this through the use of two tables stored inside the motherboard chipset called ACPI tables.
The ACPI is the first mechanism responsible for managing the memory access of peripherals as well as the organization of RAM. It does this by providing two tables to the operating system which have the same function. These tables are:
- RSDT (Root System Descriptor Table).
- XSDT (Extended Root System Descriptor Table).
If the operating system is 32 bit, it will give you the RSDT, if it is 64 bit, the XSDT. From there, the operating system will already have everything it needs to manage memory access with the processor.
The operating system is monarch
In memory addressing, there is a series of bits which applications cannot use and whose access is totally prohibited. In reality, requests for hardware resources are not made by the applications themselves, but by the operating system. No application can therefore touch the bit that disables access to protected memory without permission from the operating system itself.
This causes a series of memory access problems in virtualized systems, which leads to having to add extra bits in virtual memory addressing, which serves to indicate to the CPU a special privilege level for applications. executed in a virtual machine.
To do this, not only must the CPU be equipped with this possibility, but it also influences the way in which the operating system is organized. Cloud operating systems typically run a hypervisor, which is responsible for managing RAM access for different virtual machines.
Table of Contents